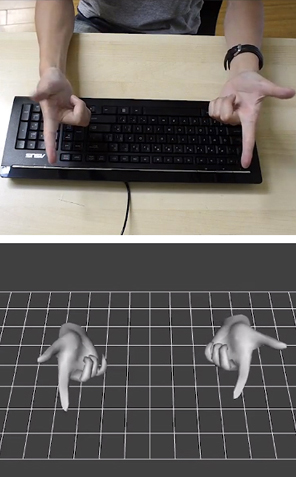
Finger mouse: 3Gear uses depth-sensing cameras to track finger movements.
3Gear Systems
Entries tagged as softwareRelated tags 3d camera flash game hardware headset history mobile mobile phone technology tracking virtual reality web wiki www 3d printing 3d scanner crowd-sourcing diy evolution facial copy food innovation&society medecin microsoft physical computing piracy programming rapid prototyping recycling robot virus advertisements ai algorythm android apple arduino automation data mining data visualisation network neural network sensors siri artificial intelligence big data cloud computing coding fft program amazon cloud ebook google kindle ad app htc ios linux os sdk super collider tablet usb API facial recognition glass interface mirror windows 8 app store open source iphone ar augmented reality army drone art car privacy super computer botnet security browser chrome firefox ieMonday, November 05. 2012Android 4.2 Announced: Photo Sphere, Gesture Typing, Multi-User, TV Connect, Quick Settings, and Much More!Via xda developpers ----- Retaining the code name from Android 4.1, 4.2 is a revamped version of Jelly Bean. Despite the lack of name change, 4.2 offers various new and exciting features. Join us as we take a closer look at some of the highlights! Photo Sphere and Camera UI Improvements Not too long ago, Google gave us native support for panoramic photos with the launch of ICS. However, in their eyes, a standard panoramic shot doesn’t properly convey the feeling of actually being there. Photo Sphere takes us one step closer. Once Photo Sphere mode is enabled, the app first guides you as you move your device to capture the entire scene. By using the same technology employed by Google Maps Street View, Photo Sphere then stitches the shots into a 360-degree view that allows you to pan and zoom, as you would in Street View. Those wishing to look at photo spheres from photographers around the would can do so as well. In addition to Photo Sphere, the Camera app’s UI also been updated with gesture controls. Thanks to the gestures, the interface no longer obscures the photo being taken with various controls. Instead, the app now makes full use of the screen real estate so that you can take better photos.
Gesture Typing Taking a page from Swype’s play book, the new keyboard built into Android 4.2 has slide gesture functionality. The heavily revised keyboard differentiates itself from current versions of Swype, however, by showing predictions in real time, as you slide around your fingers. This isn’t the first time we’ve seen real time gesture recognition—dubstep aside. That said, the interface looks to be better on Google’s latest offering, but the real test will be in actual day to day usage. The dictionaries have also been updated, as has voice recognition.
Multi-User Remember all the buzz about enabling multi-user support on Android? Apparently, Google does too. We all knew this was coming; it was only a matter of “when.” Well, it’s finally here. Multi-User support has finally made its way to the OS officially. Each user is given his or her own personal space, complete with a customized home screen, background, widgets, apps, and games. While we don’t have access to the source code to verify, this is likely accomplished by sectioning off the /data partition between users. Interestingly, switching between user profiles is done via fast user switching, rather than completely logging in and out. Naturally, this feature is only available / practical on tablets, but you can bet your bacon that this will find its way to phones in the coming months, after 4.2 is released to AOSP.
TV Connect
While we can’t speak in regards to additional functionality for Google’s enigmatic black orb, we can say that this will truly be a useful feature if executed properly. The underlying technology is the new industry standard Miracast, which was created by the Wi-Fi Alliance, and is based on Wi-Fi Direct.
DayDream A fun, new feature present in 4.2 allows your device to display photo albums, news, and more when your device is docked.
Quick Settings Remember AP’s video showing the “future site of quick settings?” It’s finally here. Google has now added a separate panel to the notification bar that can be accessed by a two-finger swipe from the top of the screen or simple button tap in the upper right corner if the notification tray is extended. Once summoned, it gives you quick access to user accounts, brightness, device settings, WiFi, Airplane Mode, Bluetooth, Battery, and Wireless Display. Lock Screen Widgets Much as we have seen in third party applications, Android now natively supports widgets on the lock screen. In fact, you can now add several pages of widgets to your device’s lock screen, essentially giving you a home screen—before you get to your home screen. Memetastic. Enhanced Google Now Google Now was also updated with more cards. A good example of this is how the software can pick out shipping updates and flight details from your email, and display them in a context-relevant manner. This, however, is not exclusively tied with the updated OS, as those with devices running 4.1 can access the update today.
Friday, November 02. 2012U.S. looks to replace human surveillance with computersVia c|net ----- Security cameras that watch you, and predict what you'll do next, sound like science fiction. But a team from Carnegie Mellon University says their computerized surveillance software will be capable of "eventually predicting" what you're going to do.
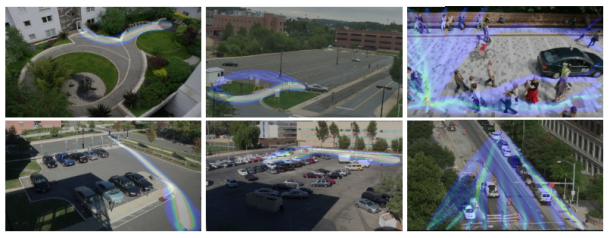
Computerized surveillance can predict what people will do next -- it's called "activity forecasting" -- and eventually sound the alarm if the action is not permitted. Click for larger image. (Credit: Carnegie Mellon University)Computer software programmed to detect and report illicit behavior could eventually replace the fallible humans who monitor surveillance cameras. The U.S. government has funded the development of so-called automatic video surveillance technology by a pair of Carnegie Mellon University researchers who disclosed details about their work this week -- including that it has an ultimate goal of predicting what people will do in the future. "The main applications are in video surveillance, both civil and military," Alessandro Oltramari, a postdoctoral researcher at Carnegie Mellon who has a Ph.D. from Italy's University of Trento, told CNET yesterday. Oltramari and fellow researcher Christian Lebiere say automatic video surveillance can monitor camera feeds for suspicious activities like someone at an airport or bus station abandoning a bag for more than a few minutes. "In this specific case, the goal for our system would have been to detect the anomalous behavior," Oltramari says. Think of it as a much, much smarter version of a red light camera: the unblinking eye of computer software that monitors dozens or even thousands of security camera feeds could catch illicit activities that human operators -- who are expensive and can be distracted or sleepy -- would miss. It could also, depending on how it's implemented, raise similar privacy and civil liberty concerns. 
Alessandro Oltramari, left, and Christian Lebiere say their software will "automatize video-surveillance, both in military and civil applications." (Credit: Carnegie Mellon University)A paper (PDF) the researchers presented this week at the Semantic Technology for Intelligence, Defense, and Security conference outside of Washington, D.C. -- today's sessions are reserved only for attendees with top secret clearances -- says their system aims "to approximate human visual intelligence in making effective and consistent detections." Their Army-funded research, Oltramari and Lebiere claim, can go further than merely recognizing whether any illicit activities are currently taking place. It will, they say, be capable of "eventually predicting" what's going to happen next. This approach relies heavily on advances by machine vision researchers, who have made remarkable strides in last few decades in recognizing stationary and moving objects and their properties. It's the same vein of work that led to Google's self-driving cars, face recognition software used on Facebook and Picasa, and consumer electronics like Microsoft's Kinect. When it works well, machine vision can detect objects and people -- call them nouns -- that are on the other side of the camera's lens. But to figure out what these nouns are doing, or are allowed to do, you need the computer science equivalent of verbs. And that's where Oltramari and Lebiere have built on the work of other Carnegie Mellon researchers to create what they call a "cognitive engine" that can understand the rules by which nouns and verbs are allowed to interact. Their cognitive engine incorporates research, called activity forecasting, conducted by a team led by postdoctoral fellow Kris Kitani, which tries to understand what humans will do by calculating which physical trajectories are most likely. They say their software "models the effect of the physical environment on the choice of human actions." Both projects are components of Carnegie Mellon's Mind's Eye architecture, a DARPA-created project that aims to develop smart cameras for machine-based visual intelligence. Predicts Oltramari: "This work should support human operators and automatize video-surveillance, both in military and civil applications." Tuesday, October 16. 2012Google must change privacy policy demand EU watchdogsVia Slash Gear -----
European data protection regulators have demanded Google change its privacy policy, though the French-led team did not conclude that the search giant’s actions amounted to something illegal. The investigation, by the Commission Nationale de l’Informatique (CNIL), argued that Google’s decision to condense the privacy policies of over sixty products into a single agreement – and at the same time increase the amount of inter-service data sharing – could leave users unclear as to how different types of information (as varied as search terms, credit card details, or phone numbers) could be used by the company.
“The Privacy Policy makes no difference in terms of processing between the innocuous content of search query and the credit card number or the telephone communications of the user” the CNIL points out, “all these data can be used equally for all the purposes in the Policy.” That some web users merely interact passively with Google products, such as adverts, also comes in for heightened attention, with those users getting no explanation at all as to how their actions might be tracked or stored.
In a letter to Google [pdf link] – signed by the CNIL and other authorities from across Europe – the concerns are laid out in full, together with some suggestions as to how they can be addressed. For instance, the search company could “develop interactive presentations that allow users to navigate easily through the content of the policies” and “provide additional and precise information about data that have a significant impact on users (location, credit card data, unique device identifiers, telephony, biometrics).” Ironically, one of Google’s arguments for initially changing its policy system was that a single, harmonized agreement would be easier for users to read through and understand. It also insisted that the data-sharing aspects were little changed from before. “The CNIL, all the authorities among the Working Party and data protection authorities from other regions of the world expect Google to take effective and public measures to comply quickly and commit itself to the implementation of these recommendations” the commission concluded. Google has a 3-4 month period to enact the changes requested, or it could face the threat of sanctions. “We have received the report and are reviewing it now” Peter Fleischer, Google’s global privacy counsel, told TechCrunch. “Our new privacy policy demonstrates our long-standing commitment to protecting our users’ information and creating great products. We are confident that our privacy notices respect European law.”
Tuesday, October 09. 2012Meet the Nimble-Fingered Interface of the Future-----
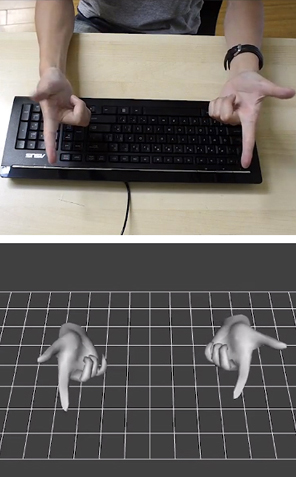
Finger mouse: 3Gear uses depth-sensing cameras to track finger movements.
Microsoft's Kinect, a 3-D camera and software for gaming, has made a big impact since its launch in 2010. Eight million devices were sold in the product's first two months on the market as people clamored to play video games with their entire bodies in lieu of handheld controllers. But while Kinect is great for full-body gaming, it isn't useful as an interface for personal computing, in part because its algorithms can't quickly and accurately detect hand and finger movements. Now a San Francisco-based startup called 3Gear has developed a gesture interface that can track fast-moving fingers. Today the company will release an early version of its software to programmers. The setup requires two 3-D cameras positioned above the user to the right and left. The hope is that developers will create useful applications that will expand the reach of 3Gear's hand-tracking algorithms. Eventually, says Robert Wang, who cofounded the company, 3Gear's technology could be used by engineers to craft 3-D objects, by gamers who want precision play, by surgeons who need to manipulate 3-D data during operations, and by anyone who wants a computer to do her bidding with a wave of the finger. One problem with gestural interfaces—as well as touch-screen desktop displays—is that they can be uncomfortable to use. They sometimes lead to an ache dubbed "gorilla arm." As a result, Wang says, 3Gear focused on making its gesture interface practical and comfortable. "If I want to work at my desk and use gestures, I can't do that all day," he says. "It's not precise, and it's not ergonomic." The key, Wang says, is to use two 3-D cameras above the hands. They are currently rigged on a metal frame, but eventually could be clipped onto a monitor. A view from above means that hands can rest on a desk or stay on a keyboard. (While the 3Gear software development kit is free during its public beta, which lasts until November 30, developers must purchase their own hardware, including cameras and frame.) "Other projects have replaced touch screens with sensors that sit on the desk and point up toward the screen, still requiring the user to reach forward, away from the keyboard," says Daniel Wigdor, professor of computer science at the University of Toronto and author of Brave NUI World, a book about touch and gesture interfaces. "This solution tries to address that." 3Gear isn't alone in its desire to tackle the finer points of gesture tracking. Earlier this year, Microsoft released an update that enabled people who develop Kinect for Windows software to track head position, eyebrow location, and the shape of a mouth. Additionally, Israeli startup Omek, Belgian startup SoftKinetic, and a startup from San Francisco called Leap Motion—which claims its small, single-camera system will track movements to a hundredth of a millimeter—are all jockeying for a position in the fledgling gesture-interface market.
Tuesday, October 02. 2012Questions abound as malicious phpMyAdmin backdoor found on SourceForge siteVia ars technica -----
 A screenshot of a system containing a
malicious backdoor that was snuck into the open-source phpMyAdmin
package. Researchers said the file date may be fraudulent. Developers of phpMyAdmin warned users they may be running a malicious version of the open-source software package after discovering backdoor code was snuck into a package being distributed over the widely used SourceForge repository. The backdoor contains code that allows remote attackers to take control of the underlying server running the modified phpMyAdmin, which is a Web-based tool for managing MySQL databases. The PHP script is found in a file named server_sync.php, and it reads PHP code embedded in standard POST Web requests and then executes it. That allows anyone who knows the backdoor is present to execute code of his choice. HD Moore, CSO of Rapid7 and chief architect of the Metasploit exploit package for penetration testers and hackers, told Ars a module has already been added that tests for the vulnerability. The backdoor is concerning because it was distributed on one of the official mirrors for SourceForge, which hosts more than 324,000 open-source projects, serves more than 46 million consumers, and handles more than four million downloads each day. SourceForge officials are still investigating the breach, so crucial questions remain unanswered. It's still unclear, for instance, if the compromised server hosted other maliciously modified software packages, if other official SourceForge mirror sites were also affected, and if the central repository that feeds these mirror sites might also have been attacked. "If that one mirror was compromised, nearly every SourceForge package on that mirror could have been backdoored, too," Moore said. "So you're looking at not just phpMyAdmin, but 12,000 other projects. If that one mirror was compromised and other projects were modified this isn't just 1,000 people. This is up to a couple hundred thousand." An advisory posted Tuesday on phpMyAdmin said: "One of the SourceForge.net mirrors, namely cdnetworks-kr-1, was being used to distribute a modified archive of phpMyAdmin, which includes a backdoor. This backdoor is located in file server_sync.php and allows an attacker to remotely execute PHP code. Another file, js/cross_framing_protection.js, has also been modified." phpMyAdmin officials didn't respond to e-mails seeking to learn how long the backdoored version had been available and how many people have downloaded it. Update: In a blog post, SourceForge officials said they believe only the affected phpMyAdmin-3.5.2.2-all-languages.zip package was the only modified file on the cdnetworks mirror site, but they are continuing to investigate to make sure. Logs indicate that about 400 people downloaded the malicious package. The provider of the Korea-based mirror has confirmed the breach, which is believe to have happened around September 22, and indicated it was limited to that single mirror site. The machine has been taken out of rotation. "Downloaders are at risk only if a corrupt copy of this software was obtained, installed on a server, and serving was enabled," the SourceForge post said. "Examination of web logs and other server data should help confirm whether this backdoor was accessed." It's not the first time a widely used open-source project has been hit by a breach affecting the security of its many downstream users. In June of last year, WordPress required all account holders on WordPress.org to change their passwords following the discovery that hackers contaminated it with malicious software. Three months earlier, maintainers of the PHP programming language spent several days scouring their source code for malicious modifications after discovering the security of one of their servers had been breached. A three-day security breach in 2010 on ProFTP caused users who downloaded the package during that time to be infected with a malicious backdoor. The main source-code repository for the Free Software Foundation was briefly shuttered that same year following the discovery of an attack that compromised some of the website's account passwords and may have allowed unfettered administrative access. And last August, multiple servers used to maintain and distribute the Linux operating system were infected with malware that gained root system access, although maintainers said the repository was unaffected. Monday, October 01. 2012HP launches Open webOS 1.0Via SlashGear -----
HP‘s TouchPad and Palm devices may be long and gone, but webOS (the mobile OS that these devices ran off of) has been alive and well despite its hardware extinction, mostly thanks to its open-source status. Open webOS, as its now called, went into beta in August, and now a month later, a final stable build is ready for consumption as version 1.0.
The 1.0 release offers some changes that the Open webOS team hopes will offer major new capabilities for developers. The team also mentions that over 75 Open webOS components have been delivered over the past 9 months (totaling over 450,000 lines of code), which means that Open webOS can now be ported to new devices thanks to today’s 1.0 release. In the video below, Open webOS architect Steve Winston demoes the operating system on a HP TouchSmart all-in-one PC. He mentions that it took the team just “a couple of days” to port Open webOS to the PC that he has in front of him. The user interface doesn’t seem to be performing super smoothly, but you can’t really expect more out of a 1.0 release.
Winston says that possible uses for Open webOS include kiosk applications in places like hotels, and since Open webOS is aimed to work on phones, tablets, and PCs, there’s the possibility that Open webOS could become an all-in-one solution for kiosk or customer service platforms for businesses. Obviously, version 1.0 is just the first step, so the Open webOS team is just getting started with this project and they expect to only improve on it and add new features as time goes on. Monday, September 24. 2012Get ready for 'laptabs' to proliferate in a Windows 8 worldVia DVICE -----
Image Credit: Stewart Wolpin/DVICE A few months after the iPad came out, computer makers who had made convertible laptops started phasing them out, believing the iPad usurped their need. What's old is new again: several computer makers are planning to introduce new Windows 8 convertible laptops soon after Microsoft makes the OS official on October 26. I agree with the assessment that the iPad stymied the need for convertible laptops; if you need a keyboard with the lighter-than-a-convertible iPad, or even an Android tablet, you could buy an auxiliary Bluetooth QWERTY keypad. In fact, your bag would probably be lighter with an iPad and an ultrabook both contained therein, as opposed to a single convertible laptop. But if these new hybrids succeed, we can't keep calling them "convertible laptops" (for one thing, it takes too long to type). So, I'm inventing a new name for these sometimes-a-laptop, sometimes-a-tablet combo computers. "Laptabs!"It's a name I'd trademark if I could (I wish I'd made up "phablet," for instance). Please cite me if you use it. (And don't get dyslexically clever and start calling them "tablaps" — I'm claiming that portmanteau, too.) Here's the convertible rundown on the five laptabs I found during last months IFA electronics showcase in Berlin, Germany — some have sliding tops and some have detachable tabs, but they're all proper laptabs. 1. Dell XPS Duo 12 It looks like a regular clamshell at first glance, but the 12.5-inch screen pops out and swivels 360 degrees on its central horizontal axis inside the machined aluminum frame, then lies back-to-front over the keyboard to create one fat tablet. The idea isn't exactly original — the company put out a 10.1-inch Inspiron Duo netbook a few years back with the same swinging configuration, but was discontinued when the iPad also killed the netbook. 2. HP Envy X2 Here's a detachable tablet laptab with an 11.6-inch snap-off screen. Combined with its keyboard, the X2 weighs a whopping 3.1 pounds; the separated screen/tablet tips the scales at just 1.5 pounds. Its heavier-than-thou nature stems from HP building a battery into both the X2's keyboard and the screen/tablet. HP didn't have a battery life rating, only saying the dual configuration meant it will be naturally massive. 3. Samsung ATIV Smart PC/Smart PC Pro Like the HP, Samsung's offering has an 11.6-inch screen that pops off the QWERTY keypad. The Pro sports an Intel Core i5 processor, measures 11.9 mm thick when closed and will run for eight hours on a single charge, while its sibling is endowed with an Intel Core i3 chip, measures a relatively svelte 9.9mm thin and operates for a healthy 13.5 hours on its battery. 4. Sony VAIO Duo 11 Isn't it odd that Sony and Dell came up with similar laptab appellations? Or maybe not. The VAIO Duo 11 is equipped with an 11.1-inch touchscreen that slides flat-then-back-to-front so it lies back-down on top of the keypad. You also get a digitizer stylus. Sony's Duo doesn't offer any weight advantages compared to an ultrabook, though, which I think poses a problem for most of these laptabs. For instance, both the Intel i3 and i5 Duo 11 editions weigh in nearly a half pound more than Apple's 11-inch Mac Book Air, and at 2.86 pounds, just 0.1 pounds lighter than the 13-inch MacBook Air. 5. Toshiba Satellite U920t Like the Sony Duo, the Satellite U920t is a back-to-front slider, but lacks the seemingly overly complex mechanism of its sliding laptab competitor. Instead, you lay the U920t's 12.5-inch screen flat, then slide it over the keyboard. While easier to slide, it's a bit thick at 19.9 mm compared to Duo 11's 17.8 mm depth, and weighs a heftier 3.2 pounds. Choices, Choices And More ChoicesSo: a light ultrabook, or a heavier laptab? And once you pop the tab top off the HP and Samsung when mobile, your bag continues to be weighed down by the keyboard, obviating the whole advantage of carrying a tablet. In other words, laptabs carry all the disadvantages of a heavier laptop with none of the weight advantages of a tablet. Perhaps there are some functionality advantages by having both; I just don't see these worth a sore back. Check out the gallery below for a closer look at each laptab written about here. All images above by Stewart Wolpin for DVICE. Tuesday, August 28. 2012The Facebook camera that can recognise you every time you walk into a shopVia Daily Mail -----

Facedeals - a new camera that can recognise shoppers from their Facebook pictures as they enter a shop, and then offer them discounts
A promotional video created to promote the concept shows drinkers entering a bar, and then being offerend cheap drinks as they are recognised. 'Facebook check-ins are a powerful mechanism for businesses to deliver discounts to loyal customers, yet few businesses—and fewer customers—have realized it,' said Nashville-based advertising agency Redpepper. They are already trialling the scheme in firms close to their office. 'A search for businesses with active deals in our area turned up a measly six offers. 'The
odds we’ll ever be at one of those six spots are low (a strip club and
photography studio among them), and the incentives for a check-in are
not nearly enticing enough for us to take the time. 'So we set out to evolve the check-in and sweeten the deal, making both irresistible. 'We call it Facedeals.' 
The Facedeal camera can identify faces when people walk in by comparing Facebook pictures of people who have signed up to the service Facebook recently hit the headlines when it bought face.com, an Israeli firm that pioneered the use of face recognition technology online. The social networking giant uses the software to recognise people in uploaded pictures, allowing it to accurately spot friends. 
The software uses a complex algorithm to find the correct person from their Facebook pictures The Facebook camera requires people to have authorised the Facedeals app through their Facebook account. This verifies your most recent photo tags and maps the biometric data of your face. The system then learns what a user looks like as more pictures are approved. This data is then used to identify you in the real world. 
In a demonstration video, the firm behind the camera showed it being used to offer free drinks to customers if they signed up to the system.
Thursday, July 26. 20125 Essential Privacy Tools For The Next Crypto WarVia Forbes ----- The first crypto war revolved around the hardware-based Clipper Chip and coercing companies to deploy broken encryption with backdoors to enable domestic State spying. Fortunately, the good guys won. The next crypto war is still a war of the government against its own citizens but this time enlisting the corporations, including social networks, as direct agents of the State. What some have dubbed Crypto Wars 2.0 manifests itself in the current litany of legislative acronyms designed to confuse and befuddle. Sometimes I think legislative bills are named with a Twitter hashtag in mind. Although it doesn’t always work out favorably for the name deciders, hashtags do generally assist in the coalescing of Internet organizers around the world. Since passage of the Cyber Intelligence Sharing and Protection Act by the U.S. House of Representatives in April, #CISPA has been everywhere. Thankfully, twin legislative initiatives SOPA and PIPA were dropped in January. Also, let’s not forget the gradual expansion of CALEA and the Lieberman-Collins Cyber Security Act and the NSA-centric McCain Cybersecurity Act. Even the seemingly unpatriotic USA PATRIOT Act of 2001 is a garbled backronym that would make George Orwell proud: Uniting (and) Strengthening America (by) Providing Appropriate Tools Required (to) Intercept (and) Obstruct Terrorism Act. The Electronic Frontier Foundation recently posted an FAQ arguing that CISPA would allow companies to review and then to hand over customers’ personal information, logs, and email to the government. That is a fairly broad and comprehensive mandate. What has gone largely unnoticed in this torrent of analysis, however, is that privacy tools for individuals already exist and they have so for many years! Quietly anticipating encroachment against basic Internet liberties, concerned cyber privacy advocates has been coding and releasing the tools that allow for private electronic communication and private web surfing. Proposed legislation like CISPA may or may not pass and become law, but if it does we have to understand the new landscape. Your privacy is up to you! 1. Email Privacy – Naked email is like a postcard for anyone to read. Pretty Good Privacy (PGP), an open source software program created by Phil Zimmermann in 1991, is the global standard for point-to-point encrypted and authenticated email. Hushmail is an OpenPGP-compatible web-based email platform that does not have access to your user password for decryption. Both products, when used correctly, offer subpoena-proof email communication. 2. File Privacy – Your files might be stored in the encrypted cloud but that doesn’t mean that they’re 100% safe for your eyes only. Free and open-source TrueCrypt allows you to encrypt folders or entire drives locally prior to syncing with Dropbox. BoxCryptor also facilitates local file encryption prior to cloud uploading and it comes with added compatibility for Android and iOS. There is an alternative to the dual-application process described above. Although most cloud-based storage services transfer over an encrypted session and store data in an encrypted form, the files are still accessible to the service provider which makes the data vulnerable to court-ordered subpoena. In order to rectify this, two different zero-knowledge data storage companies provide secure online data backup and syncing – SpiderOak and Wuala. For obvious reasons, there is no password recovery and employees have zero access to your data. 3. Voice Privacy – Wiretapping will become more prevalent in the days and months ahead. From the creator of PGP, Zfone is a new secure VoIP phone software product utilizing a protocol called ZRTP which lets you make encrypted phone calls over the Internet. The project’s trademark is “whisper in someone’s ear from a thousand miles away.” You can listen to Zimmermann present Zfone at DEFCON 15. Also utilizing ZRTP, open-source Jitsi provides secure video calls, conferencing, chat, and desktop sharing. Because of security issues and lawful interception, Tor Project’s Jacob Appelbaum recommends using Jitsi instead of Skype. Designed specifically for mobile devices and utilizing ZRTP, open-source RedPhone from Whisper Systems is an application that enables encrypted voice communication between RedPhone users on Android. 5. Traffic Privacy – The final step in the process is geo-privacy, which refers to the protection of ‘information privacy’ with regard to geographic information. Virtual Private Networks, or VPNs, have been used consistently for anonymous web browsing and IP address masking. Just make sure that your VPN provider does not log IP addresses and that they accept a form of payment that does not link you to the transaction. Additionally, the Tor Project provides free software and an open network for privacy-oriented Internet usage. Intended to protect users’ personal freedom, privacy, and ability to conduct confidential business, Tor (The onion router) is a system that improves online anonymity by routing Internet traffic through a worldwide volunteer network of layering and encrypting servers which impedes network surveillance or traffic analysis. I encourage everyone to become familiar with these basic tools for privacy. The important disclaimer is that in order to circumvent these privacy technologies, your password can be obtained in a variety of ways that are extremely intrusive and beyond the realm of casual day-to-day usage, such as hardware keyloggers or ceiling-mounted cameras. Furthermore, browser-based cryptography carries the added risk of spoofed applets being delivered to your desktop by court order or by malicious actors but this risk can be mitigated by maintaining trusted source code locally or by verifying compiled code against a digital signature. The mission statement from Tor Project director Jacob Appelbaum still stands, “Make the metadata worthless essentially for people that are surveilling you.”
Wednesday, July 25. 2012Filed Under Cellphones, GPS IndoorAtlas uses disturbances in the (geomagnetic) force to map interiorsVia engadget -----
Interior navigation is only just coming into its own, but IndoorAtlas has developed a technology that could make it just as natural as breathing -- or at least, firing up a smartphone's mapping software. Developed by a team at Finland's University of Oulu, the method relies on identifying the unique geomagnetic field of every location on Earth to get positioning through a mobile device. It's not just accurate, to less than 6.6 feet, but can work without help from wireless signals and at depths that would scare off mere mortal technologies: IndoorAtlas has already conducted tests in a mine 4,593 feet deep. Geomagnetic location-finding is already available through an Android API, with hints of more platforms in the future. It will still need some tender loving care from app developers before we're using our smartphones to navigate through the grocery store as well as IndoorAtlas does in a video
« previous page
(Page 6 of 14, totaling 131 entries)
» next page
|
QuicksearchPopular Entries
CategoriesShow tagged entriesSyndicate This BlogCalendar
Blog Administration |
|||||||||||||||||||||||||||||||||||||||||||||||||
